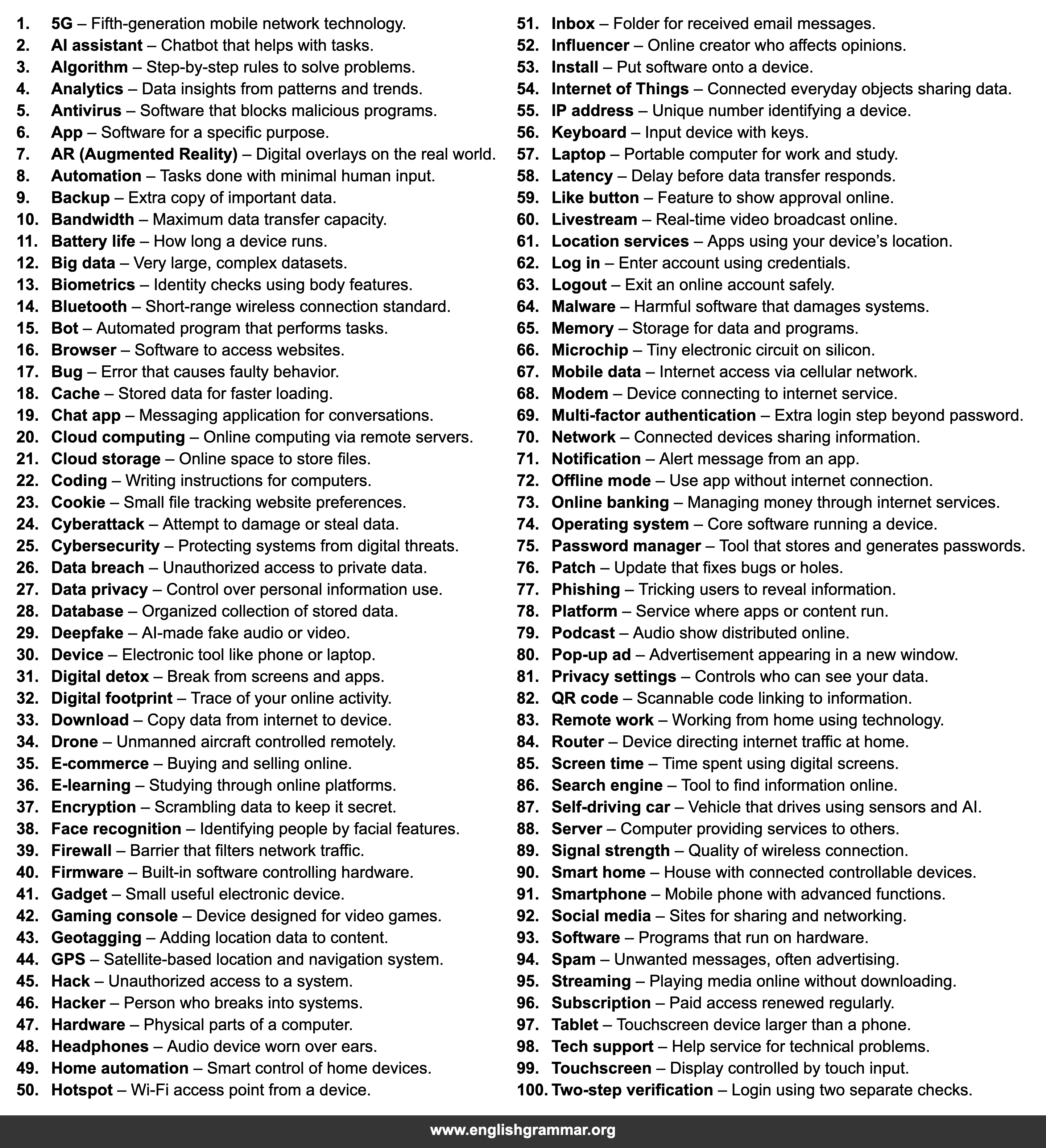
| No. | Term | Definition |
|---|---|---|
| 1. | 5G | Fifth-generation mobile network technology. |
| 2. | AI assistant | Chatbot that helps with tasks. |
| 3. | Algorithm | Step-by-step rules to solve problems. |
| 4. | Analytics | Data insights from patterns and trends. |
| 5. | Antivirus | Software that blocks malicious programs. |
| 6. | App | Software for a specific purpose. |
| 7. | AR (Augmented Reality) | Digital overlays on the real world. |
| 8. | Automation | Tasks done with minimal human input. |
| 9. | Backup | Extra copy of important data. |
| 10. | Bandwidth | Maximum data transfer capacity. |
| 11. | Battery life | How long a device runs. |
| 12. | Big data | Very large, complex datasets. |
| 13. | Biometrics | Identity checks using body features. |
| 14. | Bluetooth | Short-range wireless connection standard. |
| 15. | Bot | Automated program that performs tasks. |
| 16. | Browser | Software to access websites. |
| 17. | Bug | Error that causes faulty behavior. |
| 18. | Cache | Stored data for faster loading. |
| 19. | Chat app | Messaging application for conversations. |
| 20. | Cloud computing | Online computing via remote servers. |
| 21. | Cloud storage | Online space to store files. |
| 22. | Coding | Writing instructions for computers. |
| 23. | Cookie | Small file tracking website preferences. |
| 24. | Cyberattack | Attempt to damage or steal data. |
| 25. | Cybersecurity | Protecting systems from digital threats. |
| 26. | Data breach | Unauthorized access to private data. |
| 27. | Data privacy | Control over personal information use. |
| 28. | Database | Organized collection of stored data. |
| 29. | Deepfake | AI-made fake audio or video. |
| 30. | Device | Electronic tool like phone or laptop. |
| 31. | Digital detox | Break from screens and apps. |
| 32. | Digital footprint | Trace of your online activity. |
| 33. | Download | Copy data from internet to device. |
| 34. | Drone | Unmanned aircraft controlled remotely. |
| 35. | E-commerce | Buying and selling online. |
| 36. | E-learning | Studying through online platforms. |
| 37. | Encryption | Scrambling data to keep it secret. |
| 38. | Face recognition | Identifying people by facial features. |
| 39. | Firewall | Barrier that filters network traffic. |
| 40. | Firmware | Built-in software controlling hardware. |
| 41. | Gadget | Small useful electronic device. |
| 42. | Gaming console | Device designed for video games. |
| 43. | Geotagging | Adding location data to content. |
| 44. | GPS | Satellite-based location and navigation system. |
| 45. | Hack | Unauthorized access to a system. |
| 46. | Hacker | Person who breaks into systems. |
| 47. | Hardware | Physical parts of a computer. |
| 48. | Headphones | Audio device worn over ears. |
| 49. | Home automation | Smart control of home devices. |
| 50. | Hotspot | Wi‑Fi access point from a device. |
| 51. | Inbox | Folder for received email messages. |
| 52. | Influencer | Online creator who affects opinions. |
| 53. | Install | Put software onto a device. |
| 54. | Internet of Things | Connected everyday objects sharing data. |
| 55. | IP address | Unique number identifying a device. |
| 56. | Keyboard | Input device with keys. |
| 57. | Laptop | Portable computer for work and study. |
| 58. | Latency | Delay before data transfer responds. |
| 59. | Like button | Feature to show approval online. |
| 60. | Livestream | Real-time video broadcast online. |
| 61. | Location services | Apps using your device’s location. |
| 62. | Log in | Enter account using credentials. |
| 63. | Logout | Exit an online account safely. |
| 64. | Malware | Harmful software that damages systems. |
| 65. | Memory | Storage for data and programs. |
| 66. | Microchip | Tiny electronic circuit on silicon. |
| 67. | Mobile data | Internet access via cellular network. |
| 68. | Modem | Device connecting to internet service. |
| 69. | Multi-factor authentication | Extra login step beyond password. |
| 70. | Network | Connected devices sharing information. |
| 71. | Notification | Alert message from an app. |
| 72. | Offline mode | Use app without internet connection. |
| 73. | Online banking | Managing money through internet services. |
| 74. | Operating system | Core software running a device. |
| 75. | Password manager | Tool that stores and generates passwords. |
| 76. | Patch | Update that fixes bugs or holes. |
| 77. | Phishing | Tricking users to reveal information. |
| 78. | Platform | Service where apps or content run. |
| 79. | Podcast | Audio show distributed online. |
| 80. | Pop-up ad | Advertisement appearing in a new window. |
| 81. | Privacy settings | Controls who can see your data. |
| 82. | QR code | Scannable code linking to information. |
| 83. | Remote work | Working from home using technology. |
| 84. | Router | Device directing internet traffic at home. |
| 85. | Screen time | Time spent using digital screens. |
| 86. | Search engine | Tool to find information online. |
| 87. | Self-driving car | Vehicle that drives using sensors and AI. |
| 88. | Server | Computer providing services to others. |
| 89. | Signal strength | Quality of wireless connection. |
| 90. | Smart home | House with connected controllable devices. |
| 91. | Smartphone | Mobile phone with advanced functions. |
| 92. | Social media | Sites for sharing and networking. |
| 93. | Software | Programs that run on hardware. |
| 94. | Spam | Unwanted messages, often advertising. |
| 95. | Streaming | Playing media online without downloading. |
| 96. | Subscription | Paid access renewed regularly. |
| 97. | Tablet | Touchscreen device larger than a phone. |
| 98. | Tech support | Help service for technical problems. |
| 99. | Touchscreen | Display controlled by touch input. |
| 100. | Two-step verification | Login using two separate checks. |